こんにちは、LinuCエバンジェリストこと、鯨井貴博@opensourcetechです。
今回は、NGINX Plusを使ったリバースプロキシ環境を構築します。
コミニティ版のnginxと異なり、有償版のNGINX Plusではbackendサーバへの(アクティブ)ヘルスチェックやleast_time[headerやlast_byte]によるロードバランシングなどが行えるのが特徴です。
ネットワーク構成
作成するネットワーク構成は、以下の通り。
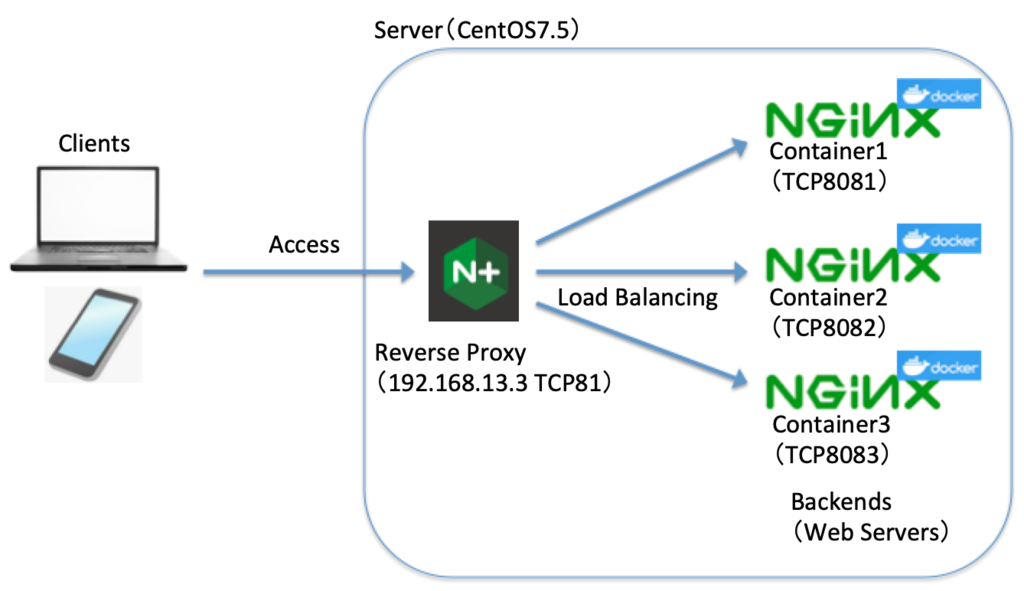
CentOS7.5上の NGINX Plusで、バックエンドサーバ(Dockerコンテナのnginx 3台)の負荷分散を行います。
バックエンドサーバの構築
なお、Dockerは yumでインストール済みです。(yum install docker)
Dockerについて知りたい方は、こちらを参照ください。
docker 〜Dockerfile を使用した、コンテナの作成・起動〜 - Opensourcetechブログ
Dockerイメージの取得
Using default tag: latest
latest: Pulling from library/nginx
Digest: sha256:31b8e90a349d1fce7621f5a5a08e4fc519b634f7d3feb09d53fac9b12aa4d991
Status: Image is up to date for nginx:latest
[root@localhost ~]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
nginx latest e81eb098537d 3 days ago 109MB
Dockerコンテナの起動
[root@localhost ~]# docker run -d -p 8081:80 -t nginx ・・・1つ目のコンテナ
d39f6d85d65f37eec0a2f7448512da45e68df6ee0b0f43a90660bc0c8d56e438
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
d39f6d85d65f nginx "nginx -g 'daemon of…" 5 seconds ago Up 3 seconds 0.0.0.0:8081->80/tcp pensive_cohen
[root@localhost ~]# docker run -d -p 8082:80 -t nginx・・・2つ目のコンテナ
0e9d799bd46a6bc36775ce2db9a2a0b9a087e572d7db91a4ed3c5087c16adbb6
[root@localhost ~]# docker run -d -p 8083:80 -t nginx・・・3つ目のコンテナ
911f5d0e2499f8d95a8c3b6cb06ff73e0fd6448606cc97dbac1c6cc6bb560c4a
[root@localhost ~]# docker ps・・・コンテナプロセスの確認
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
911f5d0e2499 nginx "nginx -g 'daemon of…" 3 seconds ago Up 2 seconds 0.0.0.0:8083->80/tcp laughing_liskov
0e9d799bd46a nginx "nginx -g 'daemon of…" 8 seconds ago Up 6 seconds 0.0.0.0:8082->80/tcp practical_boyd
d39f6d85d65f nginx "nginx -g 'daemon of…" 29 seconds ago Up 27 seconds 0.0
各コンテナ(nginx)のコンテンツファイル(index.html)を変更
root@911f5d0e2499:/# echo "Red Server" > /usr/share/nginx/html/index.html
root@911f5d0e2499:/# exit
exit
[root@localhost ~]# docker exec -it 0e9d799bd46a /bin/bash ・・・2つ目のコンテナ
root@0e9d799bd46a:/# echo "Blue Server" > /usr/share/nginx/html/index.html
root@0e9d799bd46a:/# exit
exit
[root@localhost ~]# docker exec -it d39f6d85d65f /bin/bash ・・・3つ目のコンテナ
root@d39f6d85d65f:/# echo "Green Server" > /usr/share/nginx/html/index.html
root@d39f6d85d65f:/# exit
exit
NGINX Plusの構築
続いて、フロントエンドのNGINX Plusを構築します。
なお、NGINX Plusの構築については こちらを参照ください。
NGINX Plusのインストール - Opensourcetechブログ
設定には、NGINX Plusでのみ使用可能な負荷分散アルゴリズム「least_time header;」を使ってます。
Choosing an NGINX Plus Load‑Balancing Technique - NGINX
NGINX Plusの設定(nginx.conf)
[root@localhost ~]# cat -n /etc/nginx/nginx.conf
1
2 user nginx;
3 worker_processes auto;
4
5 error_log /var/log/nginx/error.log notice;
6 pid /var/run/nginx.pid;
7
8
9 events {
10 worker_connections 1024;
11 }
12
13
14 http {
15 include /etc/nginx/mime.types;
16 default_type application/octet-stream;
17
18 log_format main '$remote_addr - $remote_user [$time_local] "$request" '
19 '$status $body_bytes_sent "$http_referer" '
20 '"$http_user_agent" "$http_x_forwarded_for"';
21
22 access_log /var/log/nginx/access.log main;
23
24 sendfile on;
25 #tcp_nopush on;
26
27 keepalive_timeout 65;
28
29 #gzip on;
30
31 #include /etc/nginx/conf.d/*.conf;
32
33 #20181120 ADD for NGINX Plus test
34 upstream nginx_containers { ・・・・バックエンドサーバの定義
35 least_time header;
36 #least_time last_byte;
37 #least_time connect;
38 #least_time first_byte;
39 server localhost:8081;
40 server localhost:8082;
41 server localhost:8083;
42 }
43
44 server { ・・・・フロントエンドの設定
45 listen 81;
46 location / {
47 proxy_pass http://nginx_containers;
48 proxy_http_version 1.1;
49 proxy_set_header Host $host:$server_port;
50 proxy_set_header X-FOrwarded-For $proxy_add_x_forwarded_for;
51 proxy_set_header X-Forwarded-Proto http;
52 proxy_ignore_client_abort on;
53 }
54 }
55
56
57 }
58
59
60 # TCP/UDP proxy and load balancing block
61 #
62 #stream {
63 # Example configuration for TCP load balancing
64
65 #upstream stream_backend {
66 # zone tcp_servers 64k;
67 # server backend1.example.com:12345;
68 # server backend2.example.com:12345;
69 #}
70
71 #server {
72 # listen 12345;
73 # status_zone tcp_server;
74 # proxy_pass stream_backend;
75 #}
76 #}
NGINX Plusの起動
[root@localhost ~]# systemctl status nginx
● nginx.service - NGINX Plus - high performance web server
Loaded: loaded (/usr/lib/systemd/system/nginx.service; disabled; vendor preset: disabled)
Active: inactive (dead)
Docs: https://www.nginx.com/resources/
[root@localhost ~]# systemctl start nginx
[root@localhost ~]# systemctl status nginx
● nginx.service - NGINX Plus - high performance web server
Loaded: loaded (/usr/lib/systemd/system/nginx.service; disabled; vendor preset: disabled)
Active: active (running) since 火 2018-11-20 19:50:37 JST; 7s ago
Docs: https://www.nginx.com/resources/
Process: 16605 ExecStart=/usr/sbin/nginx -c /etc/nginx/nginx.conf (code=exited, status=0/SUCCESS)
Process: 16588 ExecStartPre=/usr/libexec/nginx-plus/check-subscription (code=exited, status=0/SUCCESS)
Main PID: 16607 (nginx)
Tasks: 3
Memory: 4.2M
CGroup: /system.slice/nginx.service
├─16607 nginx: master process /usr/sbin/nginx -c /etc/nginx/nginx.conf
├─16608 nginx: worker process
└─16609 nginx: worker process
11月 20 19:50:37 localhost.localdomain systemd[1]: Starting NGINX Plus - high performance web server...
11月 20 19:50:37 localhost.localdomain check-subscription[16588]: Your trial subscription will expire in 22 days
11月 20 19:50:37 localhost.localdomain systemd[1]: Started NGINX Plus - high performance web server.
Firewalldの設定
NGINX Plusが使用する TCP81番ポートを解放します。
なお、Firewalldについて知りたい方は、こちらをご覧ください。
firewalldを攻略する!! - Opensourcetechブログ
Firewalldへのルール追加
[root@localhost ~]# systemctl status firewalld
● firewalld.service - firewalld - dynamic firewall daemon
Loaded: loaded (/usr/lib/systemd/system/firewalld.service; enabled; vendor preset: enabled)
Active: active (running) since 火 2018-11-20 19:31:22 JST; 4h 22min ago
Docs: man:firewalld(1)
Main PID: 664 (firewalld)
Tasks: 2
Memory: 376.0K
CGroup: /system.slice/firewalld.service
└─664 /usr/bin/python -Es /usr/sbin/firewalld --nofork --nopid
11月 20 19:57:04 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t filter -C DOCKER-ISOLATION-STAGE-2 -o docker...chain?).
11月 20 20:55:07 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C DOCKER -p tcp -d 0/0 --dport 8081 -j ...at name.
11月 20 20:55:07 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t filter -C DOCKER ! -i docker0 -o docker0 -p ...chain?).
11月 20 20:55:07 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C POSTROUTING -p tcp -s 172.17.0.2 -d 1...at name.
11月 20 20:55:27 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C DOCKER -p tcp -d 0/0 --dport 8082 -j ...at name.
11月 20 20:55:27 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t filter -C DOCKER ! -i docker0 -o docker0 -p ...chain?).
11月 20 20:55:27 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C POSTROUTING -p tcp -s 172.17.0.3 -d 1...at name.
11月 20 20:55:32 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C DOCKER -p tcp -d 0/0 --dport 8083 -j ...at name.
11月 20 20:55:32 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t filter -C DOCKER ! -i docker0 -o docker0 -p ...chain?).
11月 20 20:55:32 localhost.localdomain firewalld[664]: WARNING: COMMAND_FAILED: '/usr/sbin/iptables -w2 -t nat -C POSTROUTING -p tcp -s 172.17.0.4 -d 1...at name.
Hint: Some lines were ellipsized, use -l to show in full.
[root@localhost ~]# firewall-cmd --list-services --zone=public --permanent
ssh dhcpv6-client http
[root@localhost ~]# firewall-cmd --list-ports --zone=public --permanent
10051/tcp
[root@localhost ~]# firewall-cmd --add-port=81/tcp --zone=public --permanent ・・・TCP81番ポートの解放
success
[root@localhost ~]# firewall-cmd --list-ports --zone=public --permanent
10051/tcp 81/tcp
[root@localhost ~]# firewall-cmd --list-all-zones
block
target: %%REJECT%%
icmp-block-inversion: no
interfaces:
sources:
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
dmz
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
drop
target: DROP
icmp-block-inversion: no
interfaces:
sources:
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
external
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh
ports:
protocols:
masquerade: yes
forward-ports:
source-ports:
icmp-blocks:
rich rules:
home
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh mdns samba-client dhcpv6-client
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
internal
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh mdns samba-client dhcpv6-client
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
public (active) ・・・ここが設定変更した箇所
target: default
icmp-block-inversion: no
interfaces: enp0s3
sources:
services: ssh dhcpv6-client http
ports: 10051/tcp 81/tcp
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
trusted
target: ACCEPT
icmp-block-inversion: no
interfaces:
sources:
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
work
target: default
icmp-block-inversion: no
interfaces:
sources:
services: ssh dhcpv6-client
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
SELinuxの設定
続いて、SELinuxの設定を行います。
なお、SELinuxについて知りたい方は、こちらをご覧ください。
SELinuxのトラブルシュート(setroubleshoot / setools / sealeart) - Opensourcetechブログ
SELinuxの確認
Enforcing ・・・有効化されている
クライアントから一度 NGINX Plus(http://192.168.13.3:81)へアクセスし、コンテンツが表示されるか確認します。
大丈夫ですね。

また、念の為 SELinuxで問題がないかを確認しておきます。
[root@localhost ~]# sealert -a /var/log/audit/audit.log
4% donetype=AVC msg=audit(1538752315.786:196): avc: denied { create } for pid=10317 comm="zabbix_server" name="zabbix_server_preprocessing.sock" scontext=system_u:system_r:zabbix_t:s0 tcontext=system_u:object_r:zabbix_var_run_t:s0 tclass=sock_file
**** Invalid AVC allowed in current policy ***
type=AVC msg=audit(1538752315.788:197): avc: denied { create } for pid=10316 comm="zabbix_server" name="zabbix_server_alerter.sock" scontext=system_u:system_r:zabbix_t:s0 tcontext=system_u:object_r:zabbix_var_run_t:s0 tclass=sock_file
**** Invalid AVC allowed in current policy ***
type=AVC msg=audit(1538752326.144:203): avc: denied { create } for pid=10382 comm="zabbix_server" name="zabbix_server_preprocessing.sock" scontext=system_u:system_r:zabbix_t:s0 tcontext=system_u:object_r:zabbix_var_run_t:s0 tclass=sock_file
**** Invalid AVC allowed in current policy ***
type=AVC msg=audit(1538752336.394:208): avc: denied { create } for pid=10434 comm="zabbix_server" name="zabbix_server_preprocessing.sock" scontext=system_u:system_r:zabbix_t:s0 tcontext=system_u:object_r:zabbix_var_run_t:s0 tclass=sock_file
.
.
.
省略
.
.
.
**** Invalid AVC allowed in current policy ***
type=AVC msg=audit(1538928702.727:153): avc: denied { name_connect } for pid=2871 comm="httpd" dest=10051 scontext=system_u:system_r:httpd_t:s0 tcontext=system_u:object_r:zabbix_port_t:s0 tclass=tcp_socket
**** Invalid AVC allowed in current policy ***
type=AVC msg=audit(1538930143.707:156): avc: denied { name_connect } for pid=2870 comm="httpd" dest=10051 scontext=system_u:system_r:httpd_t:s0 tcontext=system_u:object_r:zabbix_port_t:s0 tclass=tcp_socket
**** Invalid AVC allowed in current policy ***
100% done
found 0 alerts in /var/log/audit/audit.log ・・・問題なし!
サービスの自動起動
NGINX Plus、及びdockerの自動起動設定を行います。
[root@localhost ~]# systemctl is-enabled nginx
disabled
[root@localhost ~]# systemctl enable nginx
Created symlink from /etc/systemd/system/multi-user.target.wants/nginx.service to /usr/lib/systemd/system/nginx.service.
[root@localhost ~]# systemctl is-enabled nginx
enabled
[root@localhost ~]# systemctl is-enabled docker
disabled
[root@localhost ~]# systemctl enable docker
Created symlink from /etc/systemd/system/multi-user.target.wants/docker.service to /usr/lib/systemd/system/docker.service.
[root@localhost ~]# systemctl is-enabled docker
enabled
これにて、構築完了です!!